Current asymmetric cryptosystems are based on difficult math problems that take classical computers decades to break. Functional quantum computers, while not yet existent, would be able to solve these problems much quicker. This would break the security of current cryptosystems, and render asymmetric security on the internet obsolete. For this reason, it is important to develop problems that are impossible to reduce using quantum algorithms such as Shor's (Shor) and Grover's (Grover) algorithms. Preliminary data collection was performed on a home PC. The preliminary algorithm was a primitive LWE algorithm written in Rust, with insecure parameters and no numerical optimization. It showed that an implementation of a quantum-resistant algorithm written in a moderately low level programming language was feasible, though with poor performance. The final algorithm was a Rust-based RLWE implementation which used the Number Theoretic Transform for numerical optimization. Results showed statistically significant differences in speeds between the preliminary and final algorithms. Statistically significant differences between the RLWE implementation and Kyber-768 were also observed, however, both were well under the time taken by the blink of an eye. The project establishes a basis for future work on Ring-LWE based cryptosystems that may correct issues with current standardized options, such as CRYSTALS-Kyber.
Current classical cryptosystems are based on difficult math problems that have no known polynomial time solutions. This ensures that the cryptosystems cannot easily be broken. Examples of these math problems include prime factorization and the discrete log problem. However, recent developments in quantum computing threaten these systems - reductions due to algorithms like Grover's (Grover) and Shor's (Shor) algorithms lead to quicker (polynomial time) solutions to the math problems, which renders the cryptosystems obsolete. The solution to this problem is the development of new cryptosystems based on math problems that aren't susceptible to quantum attacks.
Iterative development was used to create the final code (p0syd0n 2025, 2026). The NTT was used in the RLWE implementation to quickly multiply polynomials, because it is faster than programmatically multiplying polynomials. The first procedure used for data collection was to generate a new key and run the script over again for each datapoint. Then, a Python script was written in order to optimize this procedure. Each algorithm was tested 100 times on each input data size and average speeds for encryption and decryption were recorded.
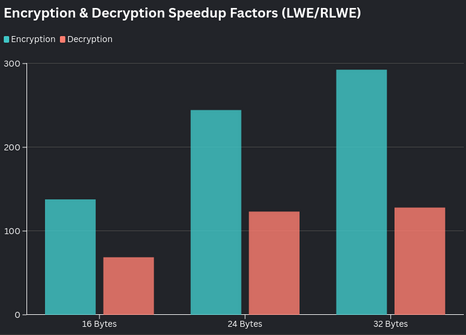
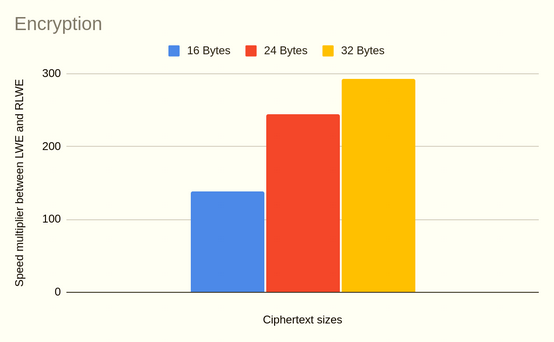
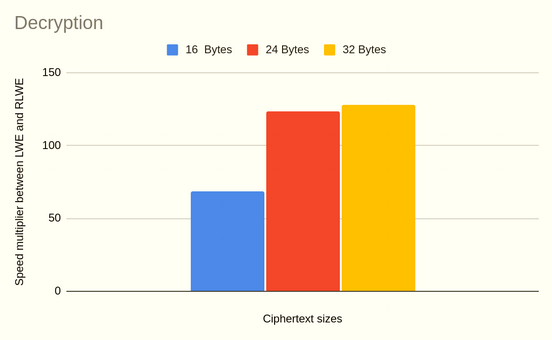
The results (averages of testing each algorithm with each size key 100 times) (Shown in Table 1 and Table 2) showed that there was a statistically significant difference between time taken by the preliminary algorithm and time taken by the final algorithm (*P1 = 0.0023 < 0.05, *P2 = 0.0074 < 0.05, where P1 is the p-value for encryption, and P2 is the p-value for decryption). The results showed that the Ring-LWE implementation which took advantage of the NTT optimization was up to 292x faster in encryption, and up to 128x faster for decryption. The results are displayed in Figure 1. Initially, data was collected manually, with subsequent data being automatically collected. There was a standard deviation of 0.114, 0.241 ms for the RLWE algorithm, and a standard deviation of 4.243, 2.121 ms for the LWE algorithm. The maximum encryption time taken was the LWE algorithm for 32 bytes of plaintext, with 326.847 ms (Table 1). The minimum encryption time taken was the RLWE algorithm for 32 bytes of plaintext, with 1.116 ms (Table 1). The maximum and minimum times for decryption were 72.844 ms (LWE) and 0.565 ms (RLWE) respectively (Table 1, Table 2). There were no outlying data points. The decryption chart has a possibly logarithmic shape (Figure 3).
The findings support the feasibility of deploying post-quantum cryptographic schemes in real-world systems, though hardware constraints remain a limiting factor. Future work includes embedded device benchmarking and side-channel resistance testing. Additionally, implementation in a language such as C would be preferred due to larger hardware capabilities.